There is a new Trojan in town and it has some business with Android users.
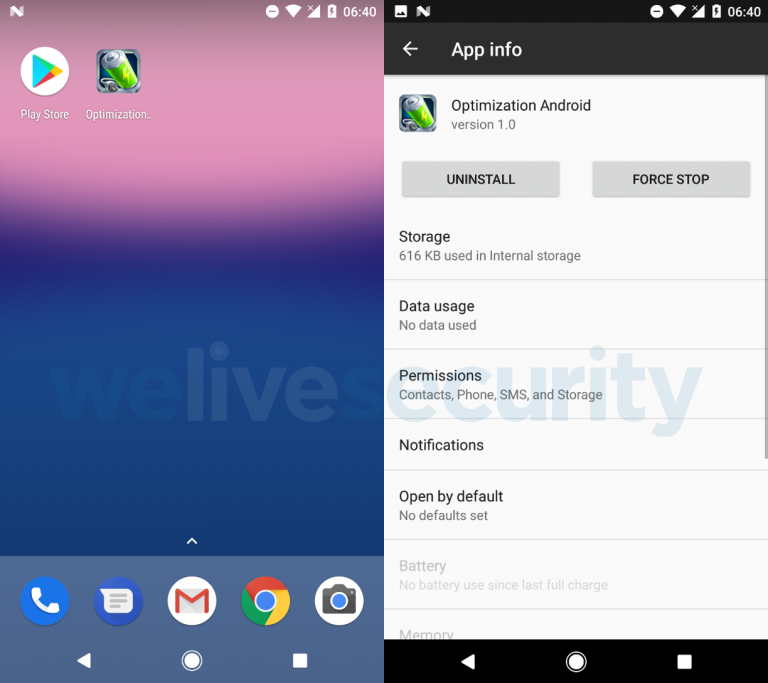
This new Trojan comes with some very unfortunate consequences. At the time this article is being written, it is known that Google Play is not one of the sources for the Trojan but that one of them is a battery optimization app distributed via third-party app stores.
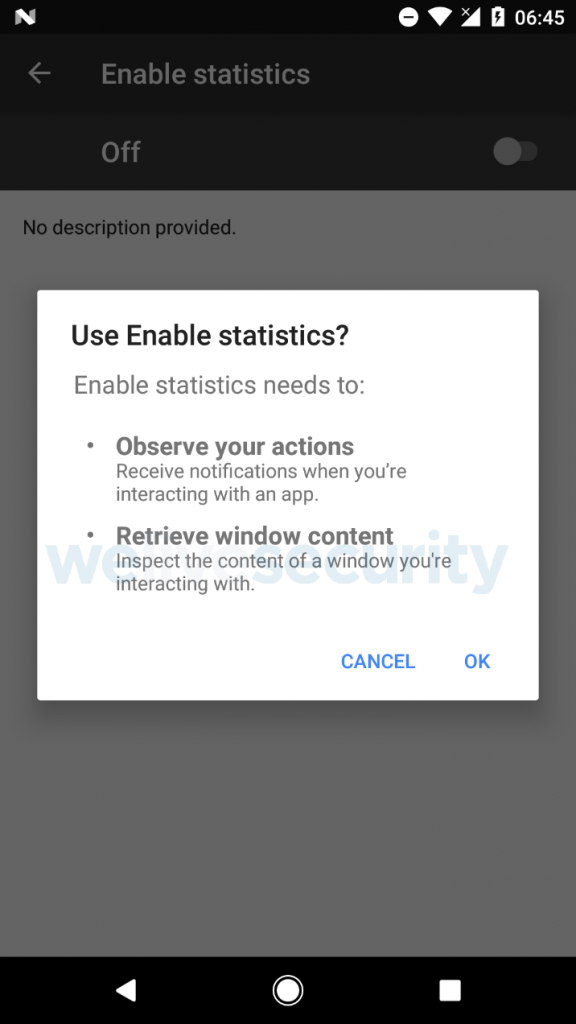
Once the app is installed, it will not open and instead simply remove the icon after it asks for access in order to “Observe your actions” and “Retrieve window content.” Afterwards, it will scan for the existence of the PayPal app but will not attempt to hack it: instead, it will lay low until the users log in themselves.
This basically means that the two factor authentication process is completely useless in this case, since it’s the user who does the logging in. This happens when the malware prompts a notification that alerts the user to launch the PayPal app.
Once the Trojan has access to the app, it will send $1000 (or the equivalent in the user’s currency) to the PayPal address of the hacker and it will continue doing so until there are no more available funds.
ESET / YouTube
The Trojan downloads HTML overlay screens for Google Play, WhatsApp, Skype, Viber, and Gmail as well and we can expect this list to expand rapidly.
But it doesn’t end here: the Trojan will also phish the Gmail password and credit card numbers via overlay attacks and will be making calls, send texts and gain access to your contacts.
Users are advised to change their internet banking password and PIN code, as well as their Gmail password and, of course, in case of any unauthorized PayPal transactions, the problem can be reported via PayPal’s Resolution Center.
At the moment, make sure you only download your apps via Google Play, just to be on the safe side.
Follow TechTheLead on Google News to get the news first.

























