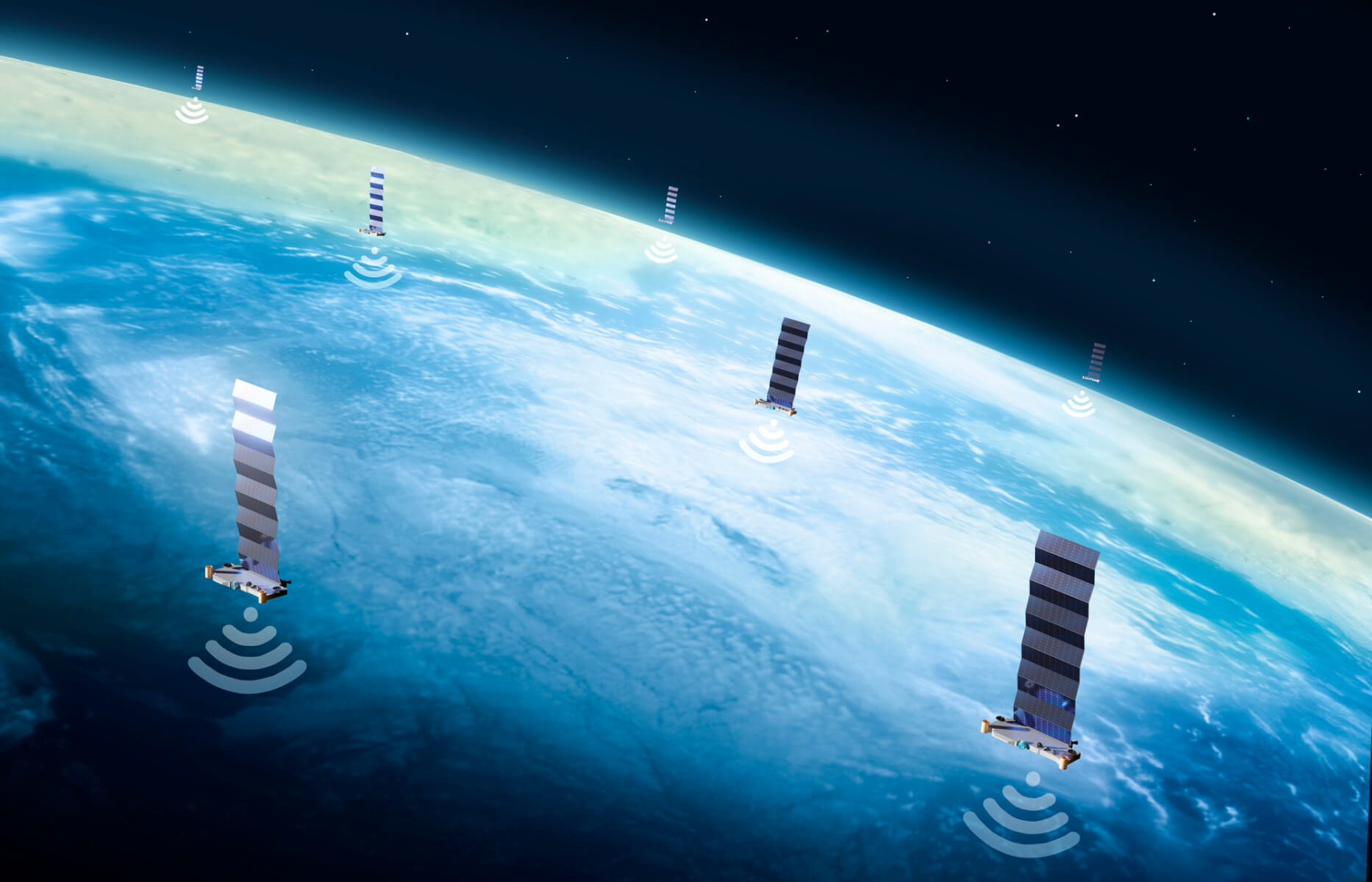
Security researcher Lennert Wouters managed to hack a Starlink terminal using only $25 in parts and he says the vulnerability is still there.
According to Wired, the researcher will take to the stage of the Black Hat security conference in Las Vegas to explain how, using incredibly cheap parts, he managed to both access Starlink’s code and run custom code on it.
“To access the satellite dish’s software, Wouters physically stripped down a dish he purchased and created a custom hacking tool that can be attached to the Starlink dish. The hacking tool, a custom circuit board known as a modchip, uses off-the-shelf parts that cost around $25. Once attached to the Starlink dish, the homemade printed circuit board (PCB) is able to launch a fault injection attack—temporarily shorting the system—to help bypass Starlink’s security protections. This “glitch” allows Wouters to get into previously locked parts of the Starlink system,” reports Wired.
Now, the tool Wouters used to hack Starlink will be available for free to anyone on Github, as well as some instructions to further test Starlink satellites.
As part of the way white hat hackers operate, Wouters already notified Starlink about these vulnerabilities and was paid by the company in thanks.
Since he told SpaceX about the attack last year, the company has issued an update to make it easier for someone to hack a Starlink device. However, according to the researchers, the vulnerability lies in the main chip and, until that is changed, all existing user terminals are vulnerable.
You can read all about the Starlink dish hack on Wired.
Tech At War: How Technology Is Helping Ukraine Fight Against Russia
Follow TechTheLead on Google News to get the news first.