In a blog post published on Wednesday last week, Moxie Marlinspike, the CEO of privacy-focused messaging app Signal, claims to have managed to hack a phone-cracking tool that is used by the British police – but also by law enforcement around the world – to extract the information stored inside seized devices.
What is Cellebrite?
Cellebrite is an Israeli digital forensics company that provides tools for the collection, analysis, and management of digital data. The company is a subsidiary of the Japanese electronics company Sun Corporation. In 2007, Cellebrite established an independent division targeted at the mobile forensics industry. The division first introduced mobile forensics products, under the family brand name ‘Universal Forensic Extraction Device’ (UFED), which have the ability to extract both physical and logical data from mobile devices, including the ability to recover deleted data and decipher encrypted and password-protected information. In 2020, Cellebrite acquired BlackBag Technologies, a forensics company with a focus on computer forensics.
Anything involving Cellebrite starts with someone else physically holding your device
These tools and the required software belong to Israeli digital intelligence firm Cellebrite, whose “Digital Intelligence Platform empowers law enforcement, governments, and enterprises to collect, review, analyze and manage digital data”, while it’s Universal Forensic Extraction Device (UFED) is being used by law enforcement worldwide in order to crack mobile phones, with the high-end tool costing approximately 6.000.
Moxie Marlinspike, whose real name is Matthew Rosenfeld, is the American entrepreneur and computer security researcher who invented Signal, and the one who recently posted the details regarding several vulnerabilities in Cellebrite’s surveillance devices.
According to Marlinspike, the software’s security is not something to write home about and sports a series of weaknesses that make it easy to be manipulated by anyone knowledgeable enough to plant inside a phone a code that would then be capable of taking over any Cellebrite hardware that would be used to scan the device in question. And from there to influencing future investigations and even rewriting the data previously saved from the tools is just a tiny step.
“We were surprised to find that very little care seems to have been given to Cellebrite’s own software security. Industry-standard exploit mitigation defenses are missing, and many opportunities for exploitation are present,” Marlinspike wrote. “Until Cellebrite is able to accurately repair all vulnerabilities in its software with extremely high confidence, the only remedy a Cellebrite user has is to not scan devices.”

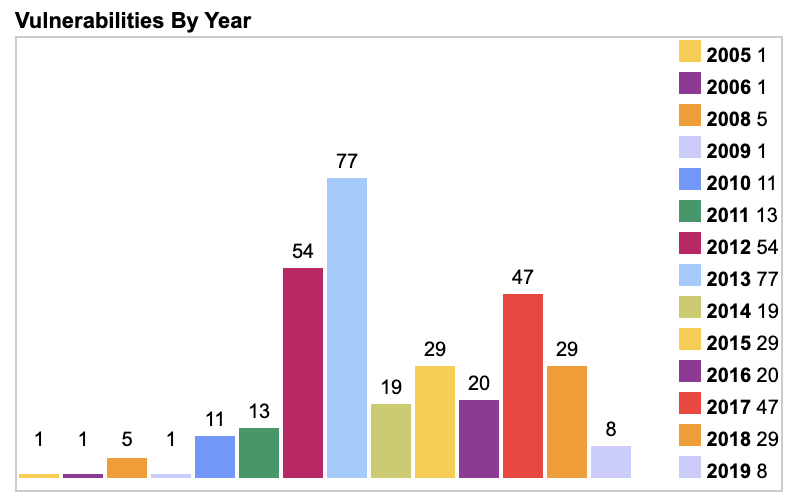
Marlinspike’s criticism of the Israeli company is not surprising considering Cellebrite’s previous unfounded claims that the company has managed to “break Signal encryption”. A 2020 blog post titled “No, Cellebrite cannot ‘break Signal encryption’” also defunded several published articles and catchy headlines such as BBC’s “Cellebrite claimed to have cracked chat app’s encryption” and called such stories “misleading and inaccurate”
“Cellebrite makes software to automate physically extracting and indexing data from mobile devices,” the Marlinspike stated. “Their customer list has included authoritarian regimes in Belarus, Russia, Venezuela, and China; death squads in Bangladesh; military juntas in Myanmar; and those seeking to abuse and oppress in Turkey, UAE, and elsewhere. Their products have often been linked to the persecution of imprisoned journalists and activists around the world, but less has been written about what their software actually does or how it works.”
And if that wasn’t enough, the blog post drops another bombshell: Cellebrite’s software appears to contain a code that might be part of Apple’s intellectual property, something the tech giant takes very seriously. And since Apple is unlikely to have granted “Cellebrite a license to redistribute and incorporate Apple DLLs in its own product” – especially considering that Apple has long been battling companies like Cellebrite, or its rival Grayshift – something like this might ultimately end up presenting “a legal risk for Cellebrite and its users.”
“Our latest blog post explores vulnerabilities and possible Apple copyright violations in Cellebrite’s software:’ Exploiting vulnerabilities in Cellebrite UFED and Physical Analyzer from an app’s perspective’ https://signal.org/blog/cellebrite-vulnerabilities/” Signal wrote in a tweet and added a video spliced with scenes from the movie famous 1995 movie ‘Hackers’.
Even though some of these findings appear to be some pretty wild claims, if they all end up being true, this could spark massive backlash and have massive ramifications for Cellebrite, which not so far ago had already been in hot water because of the use of its UFED program in the persecution of opposition in countries such as Belarus and Russia.
Follow TechTheLead on Google News to get the news first.