You have to give credit where credit is due: hackers are infinitely creative!
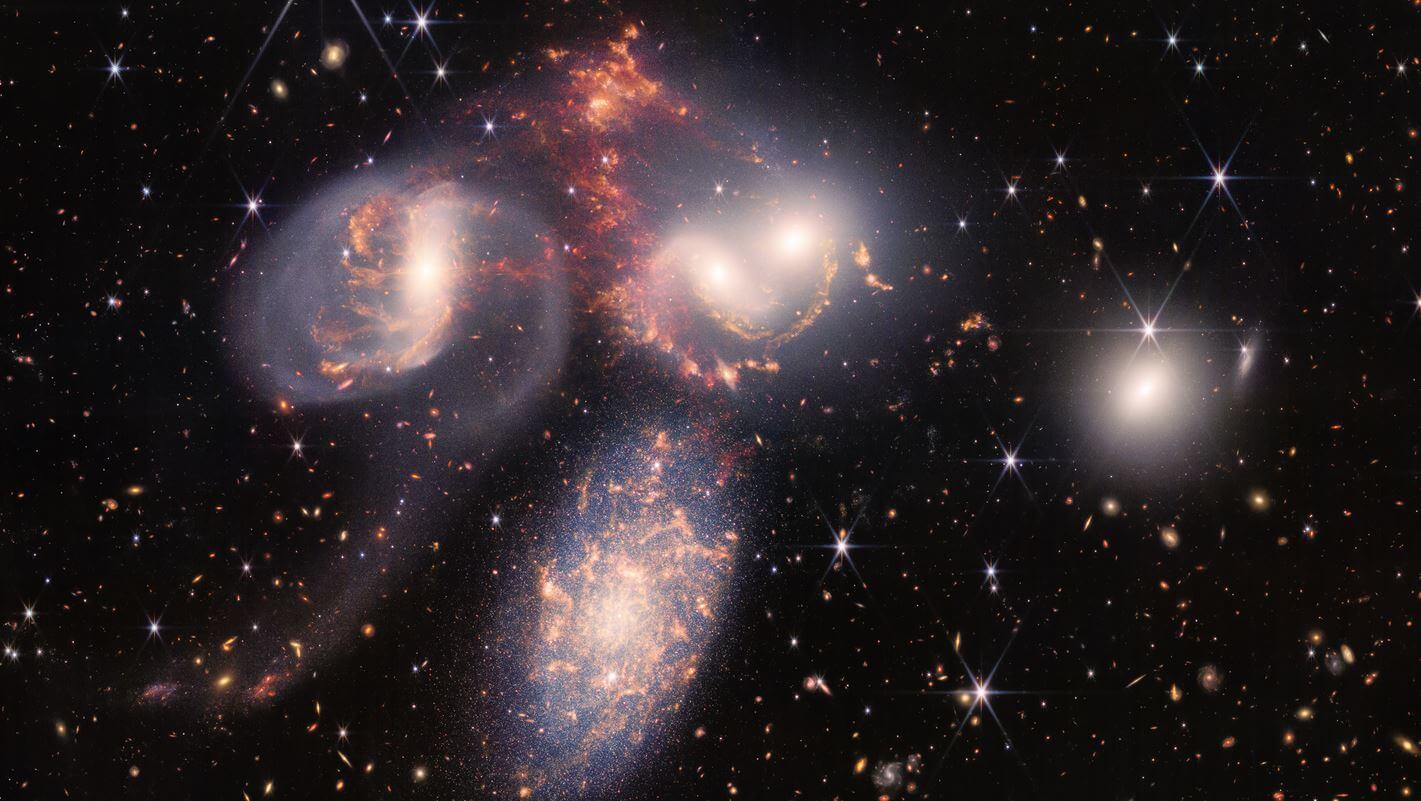
A security researcher warns of a new malware campaign that hides malicious code in images taken from the James Webb telescope.
Taking advantage of the fact that people expect a huge download when they’re looking at images released from NASA, as is the case with the James Webb Telescope incredibly-detailed photos, bad actors are now using those photos for phishing.
Security analytics platform Securonix noticed the new type of attack and called the malware campaign the GO#WEBBFUSCATOR.
How the malware attack works
As with most campaigns of this type, you usually receive a phishing email with a Microsoft Office attachment.
“Hidden within the document’s metadata is a URL that downloads a file with a script, which runs if certain Word macros are enabled. That, in turn, downloads a copy of Webb’s First Deep Field photo (pictured above) that contains as a malicious code masquerading as a certificate,” explains Engadget, who reported on Securonix’s warning.
More notably, this new malware campaign is so creative, PopSci says that using an image from the Webb Telescope “isn’t even the most fascinating aspect”, since it’s just another type of Trojan attack.
Instead, what’s interesting is that the malware is built with Go, also known as Golang, a somewhat new programming language.
“We are seeing evidence that this language is being adopted by malware developers. It makes it easier to develop cross-platform, network friendly software, which is what malware authors are developing,” said Augusto Barros, vice president at Securonix.
How to avoid malware
So, what can you do to to protect yourself against GO#WEBBFUSCATOR?
As usual, following security best practices is best.
Your email filters catch most phishing attempts but always check the full header of the email and look at the sender’s address before downloading any attachments. We also compiled a list of security tips to protect your phone from hacking that you might find helpful.
Also read: A 14-Year-Old Cracked The Codes on Australia’s New Coin In Just Over An Hour
Follow TechTheLead on Google News to get the news first.