In the wake of the recent “ad” that Intel ran on Twitter, targeting M1 Chip lacking capabilities, Apple seems to have taken a page from the classical book of good public etiquete and released a series of updates that indicate that the new MacBooks running M1 Chips will have iPhone Grade Security.
Amid increasing security concerns and exposed records due to data breaches that took place in the past months, Apple has updated its Platform Security documents on Thursday. The documents used to be separated into iOS and Mac guides but were merged by the company in December 2019 to form a single guide that details major features used by the company to protect its devices and user data across all of Apple’s platforms. This comprehensive guide has grown exponentially in the past decade, from its humble beginnings as an iOS-specific security document in 2012 to over 200 pages of technical information.
RELATED ARTICLES: New Intel Ad Slams Macs With ARM-Based M1 Chips
The newly updated document showcases some of the upgrades Apple made for iOS 14.3, iPadOS 14.3, macOS 11.1, tvOS 14.3, and watchOS 7.2, and also includes several new topics such as memory safe iBoot implementation, Boot process for a Mac with Apple silicon, Boot modes for a Mac with Apple silicon, startup disk security policy control for a Mac with Apple silicon, LocalPolicy signing-key creation, and management, signed system volume security in macOS, Apple Security Research Device, password monitoring, and IPv6 security.
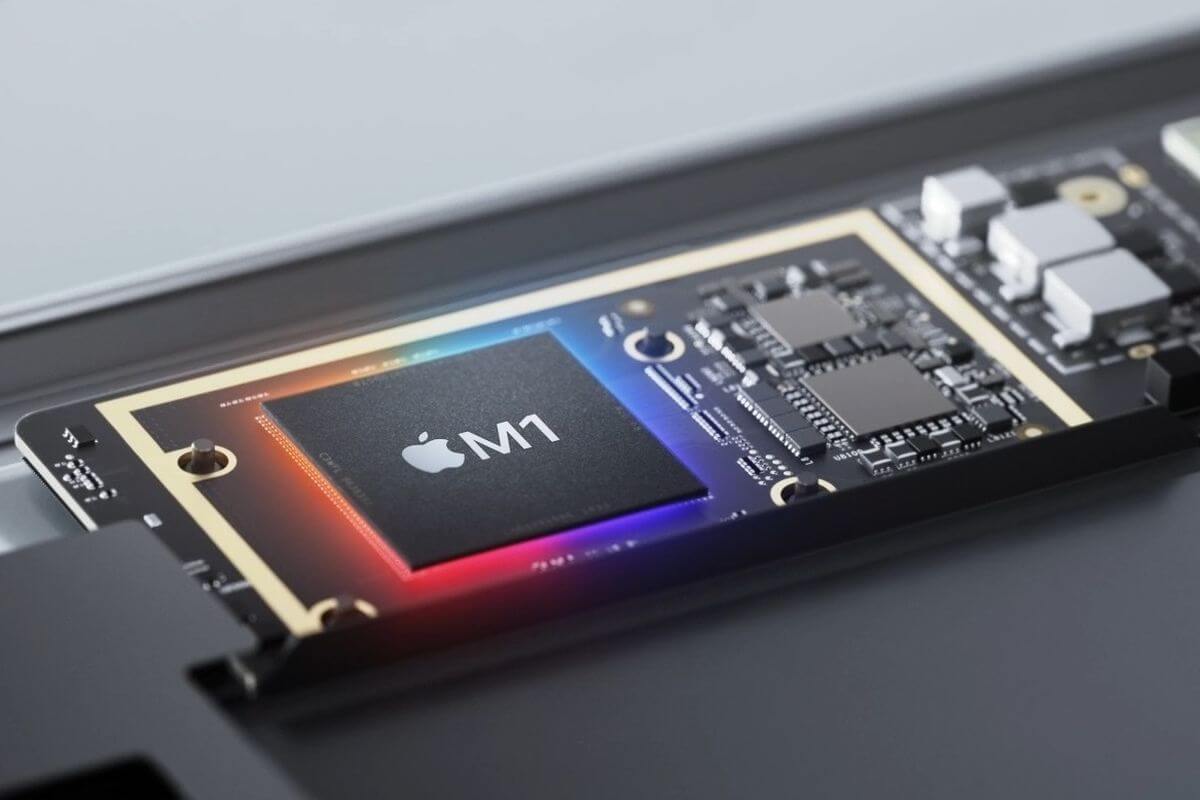
“Secure software requires a foundation of security built into the hardware,” Apple wrote in the guide update. “That’s why Apple devices — running iOS, iPadOS, MacOS, TVOS, or WatchOS – have security capabilities designed into silicon.”
The guide shares an impressive amount of information on security in general, from system security, encryption, data protection, and app security to security services, network security, and secure device management. In fact, Apple even pays as much as $1.5 million to security experts if they manage to identify possible security issues before the hackers discover and exploit them.
The included information also targets the major security improvements brought by Apple’s new M1 chips, including elements that help make the booting process more secure, but also authorization requirements that will grant access to kernel extensions (or kexts) on Macs. And this without even mentioning the built-in Secure Enclave, whose job of “protecting your login password, automatically encrypting your data, and powering file-level encryption” are all for the sole purpose of keeping users stay safe.
“Even if attacker code somehow executes, the damage it can do is dramatically reduced,” Apple confidently claims in its report.
Follow TechTheLead on Google News to get the news first.